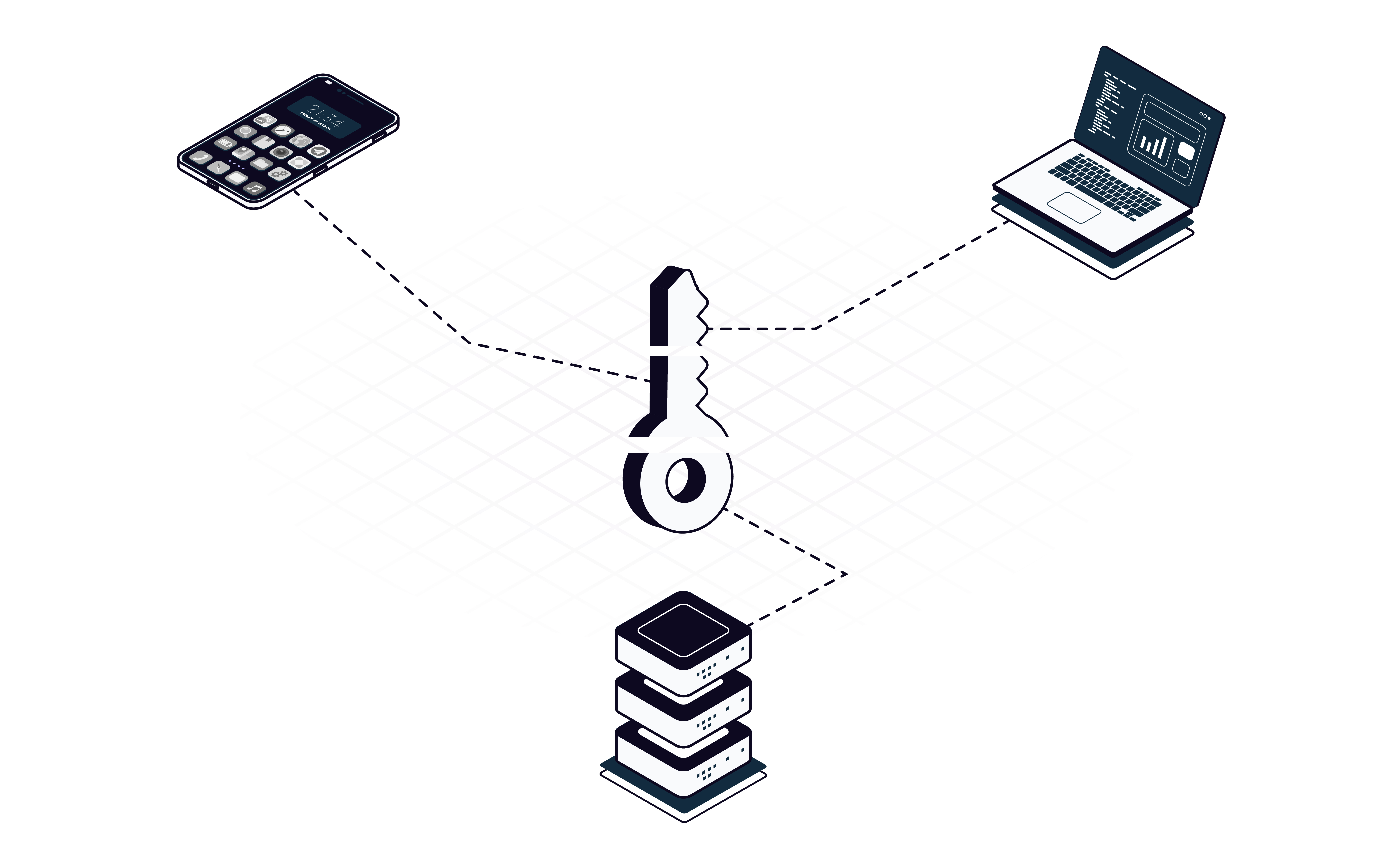
Split credentials.
Credentials are split across multiple devices, such that no device ever stores the complete cred. If attackers compromise one device, they get nothing.
SplitSecure doesn't hide or store credentials — it eliminates them. We protect secrets with architecture, not policy.
SplitSecure's architecture is secure and compliant by default, without the need for configuration or overhead. Our architecture ensures key security claims are always true in any environment.
Credentials are split across multiple devices, such that no device ever stores the complete cred. If attackers compromise one device, they get nothing.
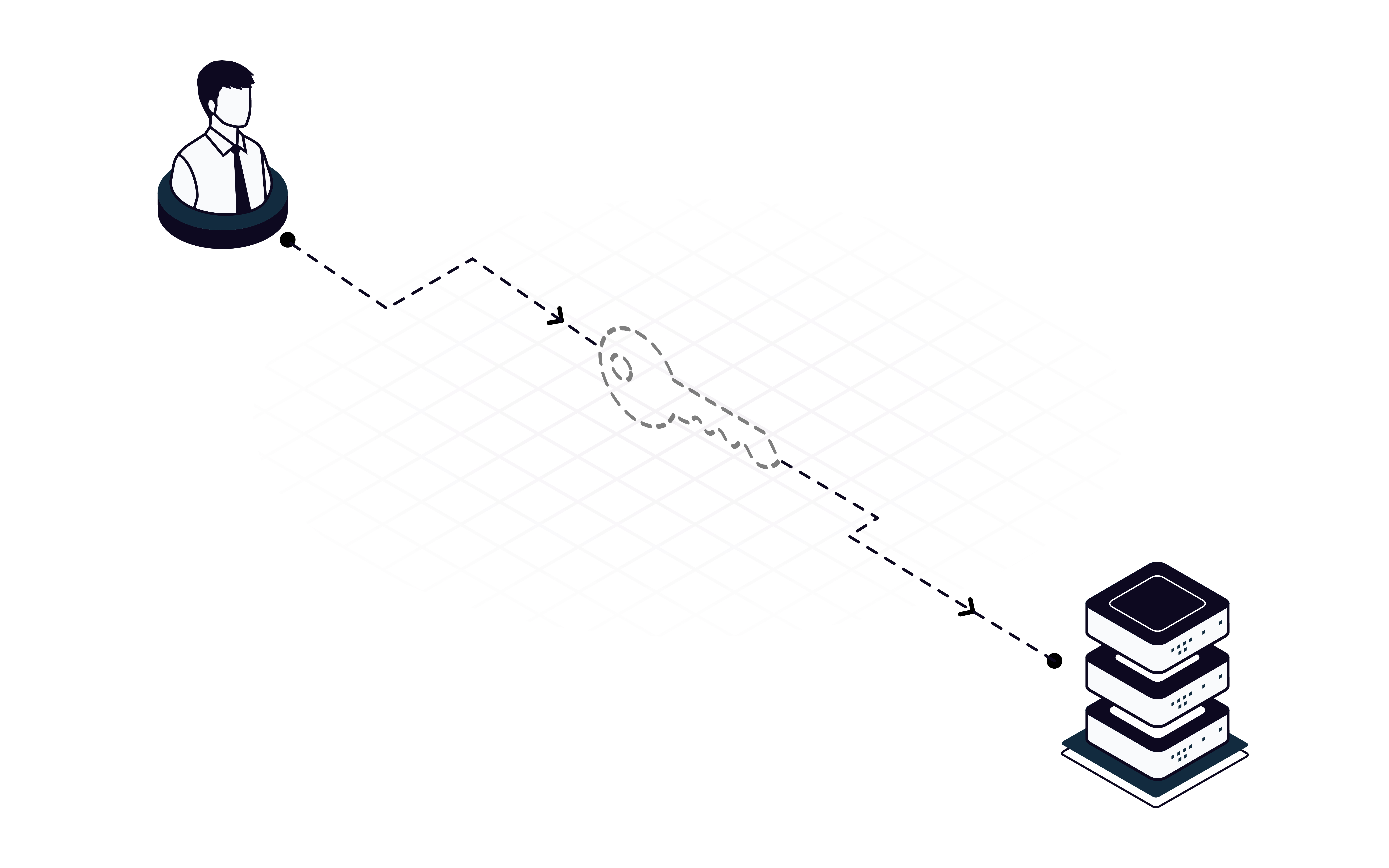
Users can log in with protected credentials normally, but the credentials are never exposed. If an employee logs in using a compromised device, the cybercriminals get nothing.
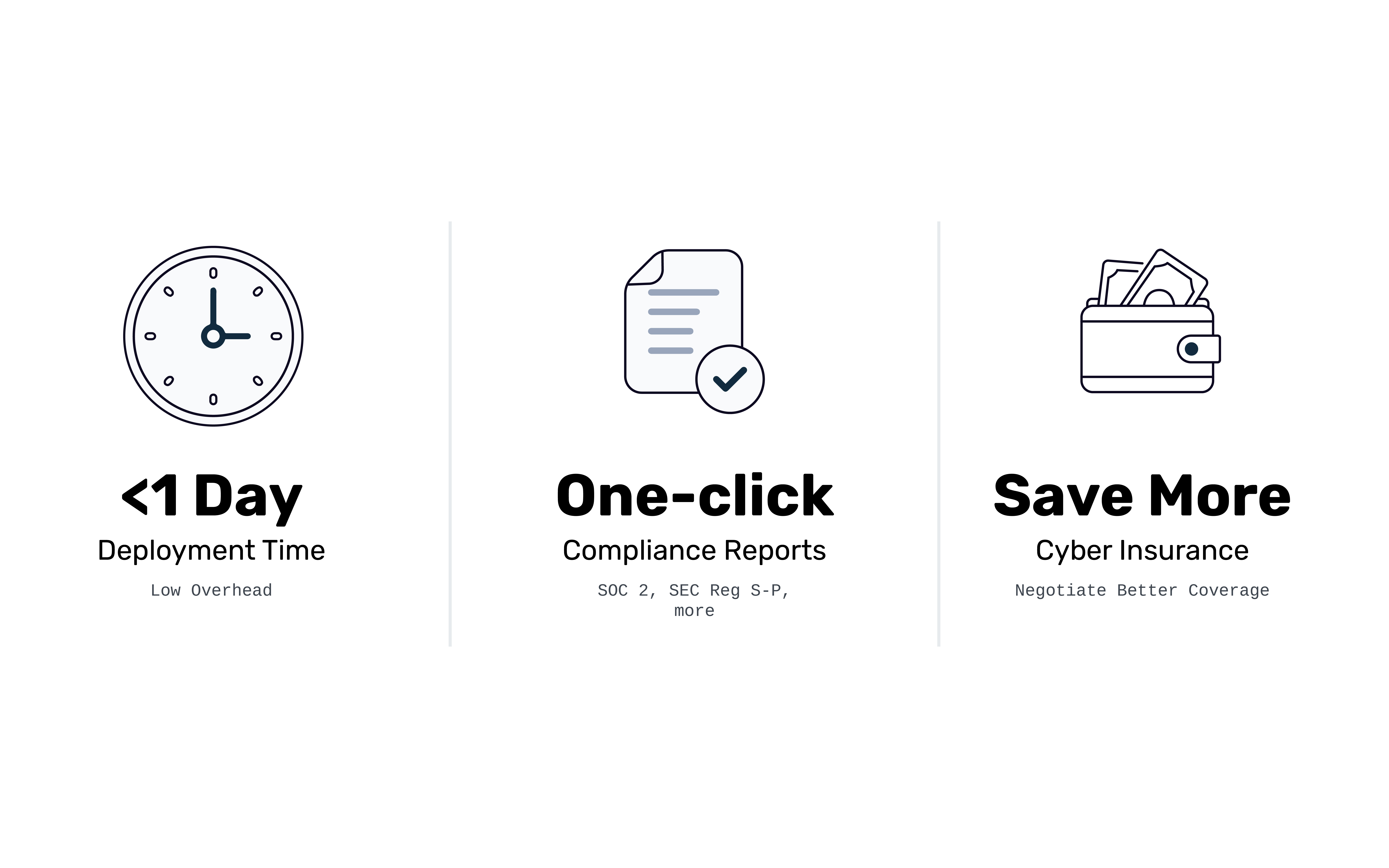
SplitSecure can be deployed in under a day and requires no dedicated support. Regulatory reports are generated with one-click, and we're compliance-ready for banks and hospitals. We can work with your cyberinsurer to get discounts for good practice.
SplitSecure's simple yet powerful security technology supports a variety of security needs.
Protect cloud accounts, admin accounts, infrastructure accounts, SSH, RDP, digital assets, and more. Support "break glass" access for emergencies.
Eliminate passwords from your organization. If you have sensitive accounts still protected by passwords, SplitSecure is the easiest way to modernize.
Implement zero standing privilege inside your organization: we eliminate risk, show compliance, and help you get discounts on cyberinsurance for demonstrated good practice.
Enable JIT elevation of privilege for sensitive actions. We support certificate management, developer workflows, finance/bank workflows, and more.
For teams that take code signing and developer privilege seriously, SplitSecure supports no-single-point-of-failure designs and multi-party approval workflows.
Streamline compliance efforts for SOC 2, ISO-27001, NIS2, DORA, SEC Reg S-P, FFIEC, or FCA Op Resilience. Reports are generated with one-click.
Watch first time setup, from a clean install to the first protected resource.
Watch how SplitSecure splits credentials across devices, lets users access protected resources without exposure, and produces compliance-ready audit logs by default.
SplitSecure is based on the S2 algorithm, a patented secret-splitting algorithm based on Shamir's Secret Sharing. The S2 algorithm makes it possible to split secrets (like credentials and keys) across multiple devices, such that no device ever persists the secret, and the secret does not have to be exposed to be used.
Because the secrets are never persisted anywhere, an attacker cannot extract them by compromising a single device or conducting a phishing attack against a single employee. Instead, they would have to compromise a critical mass of the entire storage network simultaneously, without being detected at any point in that process.
If you'd like a more in-depth overview of how the S2 algorithm works, you can contact our sales team to request a copy of our technical whitepaper.
SplitSecure is designed not to require any dedicated support. There is no configuration burden, and there is no storage that needs to be managed. In principle, the only support needed is the HR task of onboarding and offboarding users from resources, which can be largely automated.
That said, we do offer deployment and engineering support with our Enterprise plan for customers who desire it.
SplitSecure can support a wide range of compliance frameworks, including SOC 2, ISO 27001, NYDFS, DORA, SEC Reg S-O, FFIEC, NIS2, FCA Op. Resilience, HIPAA, and GDPR.
The reason we are able to support such a wide range of compliance frameworks is our secret handling technology, which ensures all secrets (including credentials) stored by SplitSecure meet all industry-standard security and regulatory requirements. Put another way, we are "compliant by default."